Docker Standalone Deployment
Use Docker Standalone for local testing or evaluation. This method runs RegScale on a single VM or laptop.
Both the Community Edition (CE) and Enterprise Edition (EE) versions of RegScale can be installed in stand-alone mode. What this means is that the application can be installed on a single machine; whether laptop, desktop, Virtual Machine (VM), or physical server.
This version is perfect for test and evaluation, small businesses, individual auditors, or other use cases where high availability and scalability are not requirements for the system.
This document provides installation files and instructions for deploying RegScale in stand-alone mode.
Local Docker
RegScale created a convenient and straightforward way to run RegScale locally, even without connecting to a remote database. This guide will allow a customer to spin up a local SQL container, connect to the database, initialize the database, and run RegScale; all within their stand-alone environment (laptop, desktop, or VM). This approach allows our customers to quickly and easily test and evaluate the product without external dependencies on infrastructure (which can take a long time to provision in Enterprise environments) and with no up-front costs for the evaluation.
NOTE: Stand-alone RegScale can also be used for Production purposes but RegScale recommends installing a production grade SQL Server database on a separate machine/environment.
In order to setup the stand-alone environment, the customer should take the following steps:
Pre-requisites
-
You need to have Docker and Docker Compose installed; the free version of Docker Desktop is sufficient
- We recommend installing on Ubuntu using the Docker Installation Guide and Docker Compose Installation Guide
-
You need to have a user account and access to Docker Hub to pull the image
-
You can review the docker container here: RegScale Docker Hub
-
If you want to test, you can manually pull the image (NOTE: We recommend pulling the latest image from the repository):
docker pull regscale/regscale:latest
-
Architecture
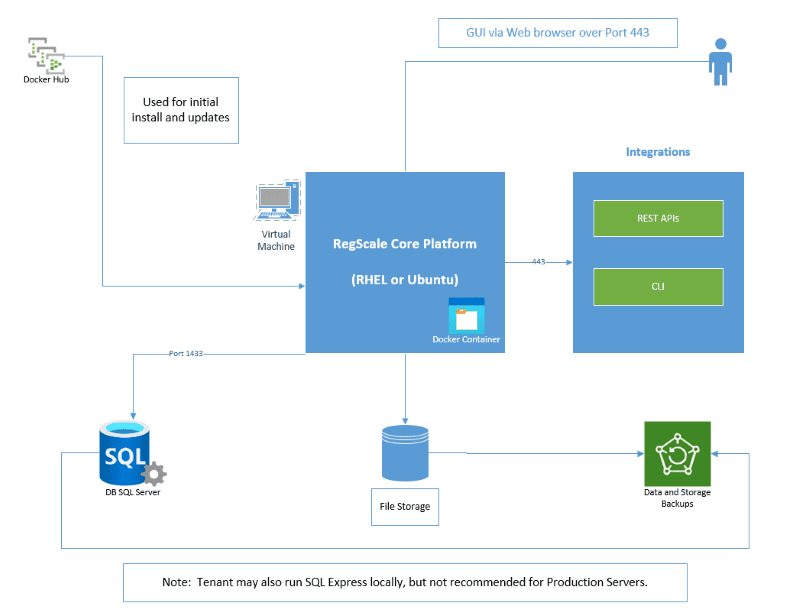
The overall components of this architecture are described below:
- RegScale Core Platform - Linux Docker Container that runs on a Virtual Machine (VM) based on Red Hat Enterprise Linux (RHEL) or Ubuntu. It can also be installed locally on a Mac laptop or Windows workstation (using the Windows Subsytem for Linux) for test and evaluation purposes. This container is the core of the application and contains the Angular front end and middle tier of C# Application Programming Interfaces (APIs)
- Docker Hub - repository that contains all published releases of RegScale containers which can be pulled for installations or upgrades
- APIs - Representational State Transfer (REST) APIs that are well defined with a published Swagger interface for developing automations and integrations
- Command Line Interface (CLI) - sidecar for bulk data processing via the command line (OPTIONAL and only available for Enterprise Customers). It should run on RHEL or Ubuntu in a separate VM which can schedule CRON jobs or other means to batch update large amounts of data.
- SQL Server - relational database for storing RegScale data. It is typically installed into an existing database cluster or a cloud Relational Database Service (RDS). For test and evaluation, you can also install a local SQL Server Express instance on the same VM but this is not recommended or supported for Production use.
- NOTE: If you are installing on an ARM MacBook (e.g. M1, M2, M3), use "Manual Mode" below and pull the specific files for ARM
- File Storage - RegScale allows customers to upload and encrypt evidence inside of the platform. Storage is needed to hold this data and is typically thin provisioned to allow expansion over time.
- Backups - both the database and file storage should be routinely backed up. The container does not need to be backed up as it is immutable and stateless.
Easy Mode Installation
The RegScale team has built an installer script to make loading RegScale as easy and fast as possible. Typical installation times are 8 - 10 minutes (NOTE: There will be a wait time while the database is seeded. The database connection will typically need a few minutes to finish the seeding process before it becomes available to serve the application. During this period, you will see connection reset errors until the process completes).
The following steps are required to install in easy mode:
- The installation script requires Python ( versions >= 3.9.0 & <=3.11) (download here)
- Recommend using a python virtual environment: See here for instructions
- The installation script requires pip (How to install pip)
- NOTE: All scripts are in our GitHub Community Repository
- Download the installation script
- Run the installer based on Operating System:
- Windows -
py standalone_regscale.py start - Mac/Linux -
python3 standalone_regscale.py start
- Windows -
- Within 8 - 10 minutes, the application should be installed and running. NOTE: During this time, the web page will show blank and will not load. Keep refreshing every few minutes until the page comes up and you see the RegScale login.
- See Post-Deployment Steps to continue
- To remove the application:
- Windows -
py standalone_regscale.py stop - Mac/Linux -
python3 standalone_regscale.py stop
- Windows -
NOTE 1: Windows may require a manual install of "pip3" if it is not present on the system
NOTE 2: Easy mode installer does not currently support providing an external database connection string but this is on the roadmap
NOTE 3: For Linux installs, only RHEL and Ubuntu have been tested and are supported
NOTE 4: For Linux installs, some commands may require sudo for permissions
NOTE 5: For Mac installs, enter sudo password if prompted
NOTE 6: The JWT key should be set explicitly by the user and use of the default key is not recommended. Also, RegScale recommends the user rotate this key periodically for security purposes. Changing the JWT signing key will invalidate all existing ServiceAccount tokens, as they will no longer be verifiable using the new key. This means that any services relying on these tokens for authentication will fail until new tokens are generated. To restore functionality, all affected ServiceAccount tokens must be recreated using the new key.
NOTE 7: The Encryption key should be set explicitly by the user and the default password should not be used. This key cannot be changed so use of a long key (64 characters) is recommended.
Manual Installation
-
Download all of the configuration files below:
- NOTE: All scripts are in our GitHub Community Repository
- RegScale Configurations
- or pull via command line:
wget https://raw.githubusercontent.com/RegScale/community/main/standalone/atlas.env
- or pull via command line:
- RegScale Database Configurations
- or pull via command line:
wget https://raw.githubusercontent.com/RegScale/community/main/standalone/db.env
- or pull via command line:
- Docker Compose Configurations
- or pull via command line:
wget https://raw.githubusercontent.com/RegScale/community/main/standalone/docker-compose.yml
- or pull via command line:
- Alternate RegScale Database Configuration for ARM
- If running the containers on an ARM-based platform, add the following line to the docker-compose.yaml file below the container name (
container_name: atlas-db):
platform: linux/amd64 - Ensure that the line is indented to match the line above it
- If running the containers on an ARM-based platform, add the following line to the docker-compose.yaml file below the container name (
- All files should in the same directory. Perform a
lscommand to verify that they are downloaded correctly.
-
Edit
db.envusingnano db.env- Set
SA_PASSWORDto a secure value of your choosing. Avoid most special characters as they will potentially cause issues (allowed special characters are listed below). NOTE: this password is stored locally with the customer and is not available or retrievable by RegScale. - NOTE This password needs to meet the built-in complexity requirements of SQL Server:
- At least 8 characters.
- The password does not contain the account name of the user.
- The password is at least eight characters long.
- The password contains characters from three of the following four categories:
- Latin uppercase letters (A through Z)
- Latin lowercase letters (a through z)
- Base 10 digits (0 through 9)
- Non-alphanumeric characters such as: exclamation point (!), dollar sign ($), number sign (#), or percent (%)
- Passwords can be up to 128 characters long. Use passwords that are as long and complex as possible.
- Set
-
Edit
atlas.envusingnano atlas.env- StoredFilesPath: This is the location where the persistent storage will be mounted. You should not need to change this value, unless you change the mount point in your
docker-composefile- Default value:
/atlas/files
- Default value:
- FileSizeLimit: The file size limit per file in bytes. Please note the overall limit is 120 MB, even if you set this variable larger than that. This variable is optional and will be set to 100 MB by default if nothing is provided.
- Default value:
104857600
- Default value:
- DB_SERVER: Name of the database server. DO NOT CHANGE IF USING docker-compose
- Default value:
atlas-db
- Default value:
- DB_PORT: Port for the database. DO NOT CHANGE IF USING docker-compose
- Default value:
1433
- Default value:
- JWTSecretKey: This is your JWT Secret Key. This can be any random hex string that is 32 characters/bytes in length (or 256 bits respectively).
- For setting keys, we recommend this password generator Online Encryption Key Generator (256 bit) for quickly generating random security keys.
- Do not include special characters in this secret
- You can use any other mechanism to create this key. However, we recommend a minimum of a 256-bit secure key as it will be changed infrequently (or never) as it will invalidate all open sessions after being deployed.
- Default value:
JWTSecretKeyFromSomeWhere6789012
- EncryptionKey: This is your Encryption Key for encrypted files and data in the database. This can be any random hex string that is 32 characters/bytes in length (or 256 bits respectively).
- For setting keys, we recommend this password generator Online Encryption Key Generator (256 bit) for quickly generating random security keys.
- Do not include special characters in this password
- You can use any other mechanism to create this key. However, we recommend a minimum of a 256-bit secure key as it will be changed infrequently (or never) as it will invalidate all encrypted files after being deployed.
- Default value:
YourEncryptionKeyFromSomeWhere12 - WARNING: Once this key is used, it should not be changed as it can result in data becoming unreadable.
- SQLConn: This is the SQL Connection string from above.
- If using the container-hosted DB, simply configure the password to match the one configured in db.env. All other components should stay the same. NOTE: If you wish to connect to an external database, you can provide a full connection string and avoid provisioning a local SQL Server Express database.
- StoredFilesPath: This is the location where the persistent storage will be mounted. You should not need to change this value, unless you change the mount point in your
Run RegScale
-
If you want to stand up the database container and RegScale, navigate into the directory where the
docker-compose.ymlfile is located-
Type:
docker-compose up- This command will start the
atlas-dbcontainer - Once the database is running, it will start the
atlascontainer - The
atlascontainer will wait for the database container to start and be listening on port 1433 - NOTE: Through this process, if you receive any permission errors, prefix commands with
sudoto ensure appropriate permissions
- This command will start the
-
To run this command in the background you can alternately run:
docker-compose up -d
-
-
If you have a database you want to point to, edit the
atlas.envwith your database connection string and ensure your DB server is listening on port 1433-
Simply run:
docker run --env-file atlas.env -v atlasvolume:/atlas/files -p 81:8080 regscale/regscale:latest -
To run any version < 5.27, expose port 80 by running:
docker run --env-file atlas.env -v atlasvolume:/atlas/files -p 81:80 regscale/regscale:5.26.1
-
-
RegScale should now be running locally on a single container.
- Point your browser to http://localhost:81
- (NOTE: Ubuntu and other OS run local firewalls by default. You may need to open port 81 on your host OS.)
-
See Post-Deployment Steps to continue
-
When you are done, you can shutdown the containers with:
docker-compose down- This will still leave the data in the database and on the volumes
Add Certificates (Stand-Alone)
When configuring the system in Stand-Alone mode, RegScale has the ability to support SSL certificates for secure/encrypted communications. These certificates can be self-signed, signed by an internal CA, or signed by an external CA. Self-signed should ONLY be used in test environments
-
Make sure RegScale is stopped:
docker-compose down -
In order for this to work, you need a certificate in PFX format. These directions should walk you through how to generate a self-signed cert on Linux or Mac
-
Download the
https.configfile: HTTPS Config File -
Run the following command to generate a private key and a certificate signing request:
openssl req -config https.config -new -out csr.pem -
Run the following command to create a self-signed certificate:
openssl x509 -req -days 365 -extfile https.config -extensions v3_req -in csr.pem -signkey key.pem -out https.crt -
Run the following command to generate a pfx file containing the certificate and the private key that you can use with RegScale. Remember the password, as we will use it later. You can also choose to not password protect this file if you desire.
openssl pkcs12 -export -out https.pfx -inkey key.pem -in https.crt -password pass:<<Password>>
-
-
Copy to the
https.pfxfile to its own directory to be mounted inside the RegScale container.- For this example, I am using
/atlas/ssl
- For this example, I am using
-
Edit the
docker-compose.ymlfile:-
Under the
atlascontainer: -
In
ports:, under the line- "81:8080", add:- "8443:443" -
In
volumes:, under the line- atlasvolume:/atlas/files, add:- /atlas/ssl:/atlas/ssl -
The FIRST
/atlas/sslis the directory on your Linux/Mac. Modify this to be the location where you have the https.pfx file. -
The SECOND
/atlas/sslis the location within the container. DO NOT CHANGE THIS.
-
-
Edit the
atlas.envfile and add the following lines to the end of the file (where PASSWORD should be changed to the password you set up earlier):ASPNETCORE_URLS=https://+:443;http://+:80 Kestrel__Certificates__Default__Path=/atlas/ssl/https.pfx Kestrel__Certificates__Default__Password=PASSWORD -
Start RegScale again:
docker-compose up -d -
Point your browser to https://localhost:8443
Remove Volumes
Please note, the Docker volumes are created and are persistent so your data will remain. If you want to REMOVE all the data or start fresh, run the following commands:
-
Verify your volume names:
docker volume ls -
You should see output similar to(or exactly like) the following:
DRIVER VOLUME NAME local docker_standalone_atlasvolume local docker_standalone_sqlvolume -
Remove both of the volumes, using the names from the command above:
docker volume rm docker_standalone_atlasvolume docker_standalone_sqlvolume
Back up and Restore Volumes
To backup the database volume for security or migration, use the docker volume commands. The following assumes that the names and labels in docker-compose.yml have not been changed.
Backup the volume from the atlas-db container:
sudo docker run --rm --volumes-from atlas-db -v $(pwd):/backup busybox tar cvf /backup/backup.tar /var/opt/mssql
This creates a tar file backup.tar in the current directory.
To restore or overwrite a atlas-db container. Run the following from the directory where the backup.tar file resides:
sudo docker run --rm --volumes-from atlas-db -v $(pwd):/backup busybox tar xvf /backup/backup.tar
Air Gap Deployments
The preceding steps require the installation target to be Internet accessible. To install RegScale on an "air-gapped" network (not connected to the Internet) the docker images will need to be copied from the Internet and loaded on a local server. There is a command line utility called "skopeo" that achieves this.
- Install skopeo (use the appropriate package manager for the local version of linux) on an internet facing machine:
sudo yum install skopeo
- Use skopeo to download the docker container images from https://docker.io:
skopeo login docker.io
<username>
<password>
skopeo copy docker://regscale/regscale:latest dir:./images/regscale
skopeo copy docker://mcr.microsoft.com/mssql/server:2019-latest dir:./images/mssql
- This will create two directories under "images": "regscale" and "mssql". Use the
tarcommand to compress these directories
tar -cvf containers.tar ./images
- Copy the containers.tar file from the internet facing computer to the air-gapped server where RegScale is to be installed using sneakernet, one-way transfer, or other approved local methods.
- On the air-gapped server, expand the tar file:
tar -xvf containers.tar
- Use the docker command to load the images:
sudo docker load -i ./images/mssql
sudo docker load -i ./images/regscale
- The Images are now available to be used by the
docker-composecommand in the above instructions
Updated 8 months ago
